Updates (April 2026 to June 2026)
April 2026 — Updated the topic to add information about the addition of change logs as an available action on exclusion rules. For more information, see Actions On Exclusions.
April 2026 — Updated the topic to include accurate behavior details for exclusion from monitoring events. For more information, see Supported Exclusion Types.
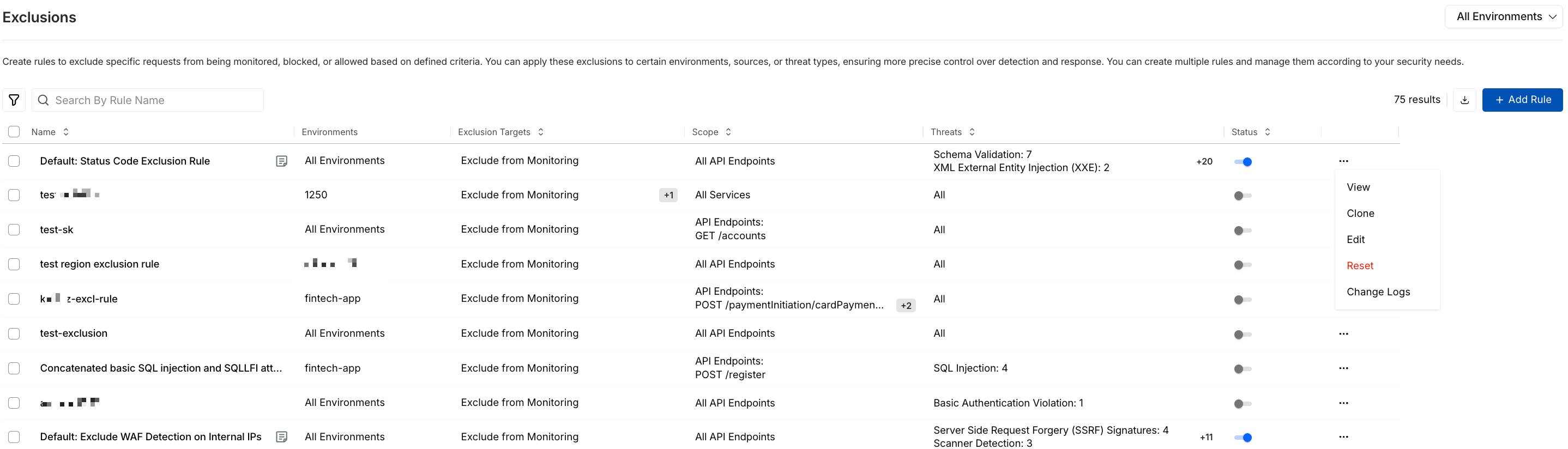
Exclusions in Traceable enable you to create rules that exclude specific requests from being monitored, blocked, or allowed based on defined criteria. You can apply these exclusions to certain environments, sources, or threat types, ensuring more precise control over detection and response. You can create multiple rules and manage them according to your security needs.
What will you learn in this topic?
By the end of this topic, you will be able to:
Understand the supported exclusion types and how to leverage them.
Learn the steps to create exclusion rules in Traceable.
Learn the actions that you can take on exclusions.
Understand Exclusions
Before you configure exclusion rules, it is important to understand how they help refine detection and enforcement by filtering out known, trusted, or non-critical traffic. The table below explains when to use exclusions, why they improve accuracy, and how to apply them effectively:
Why use it? | When to use? | How can you leverage it? |
|---|---|---|
Exclusions allow you to reduce noise, prevent unnecessary actions, and ensure that security controls remain focused on relevant threats. This improves signal clarity and ensures that security controls focus on meaningful threats. | Use exclusions when specific traffic, such as internal users, trusted partners, automated systems, or non-production environments, should not trigger detection or enforcement. They are also useful to prevent duplicate evaluations or unnecessary scoring. | Create exclusion rules by defining source criteria, payload, and targets. Select the appropriate exclusion type based on whether you want to bypass monitoring, blocking, allow actions, or scoring. Use static or dynamic payload matching for precision and continuously refine rules based on observed traffic patterns. |
Before you begin
Before you proceed to create the exclusion rules, make a note of the following:
Make sure you have the Edit and Settings RBAC permissions to create rules. For more information, see RBAC.
Make sure you have a fair understanding of payload match. Traceable supports Static Payload Match and Dynamic Payload Match in the rule creation steps. For more information, see Understand Payload Match.
Supported exclusion types
Traceable allows you to create exclusion rules based on the following exclusion types:
Exclude from Monitoring — This option prevents requests that match defined criteria from triggering threat detection or alert generation. For example, you can exclude requests associated with specific email domains, such as test-domain.com, to reduce unnecessary detections. These requests continue to be captured and available for trace analysis within the platform. However, they do not generate security events or alerts.
Exclude from Blocking — This option is useful when you do not want to block specific data from requests that match your configured criteria. For example, you can exclude data from being blocked (allow) when it comes from Hosting Provider IP types.
Exclude from Allow — This option prevents specific data from being returned for requests that match your configured criteria. For example, data from the Afghanistan region can be excluded from being allowed (blocked).
Exclude from Threat Actor Scoring — This option prevents the threat actor score from being affected for specific requests that match your configured criteria. For example, when the same request is flagged by two rules, you can exclude one to prevent scoring it twice.
Create an exclusion rule
To create an exclusion rule, navigate to Protection → Settings → Exclusions, click + Add Rule, and complete the following steps:
Create Exclusion Rule Criteria Step
Step 1 — Set the criteria
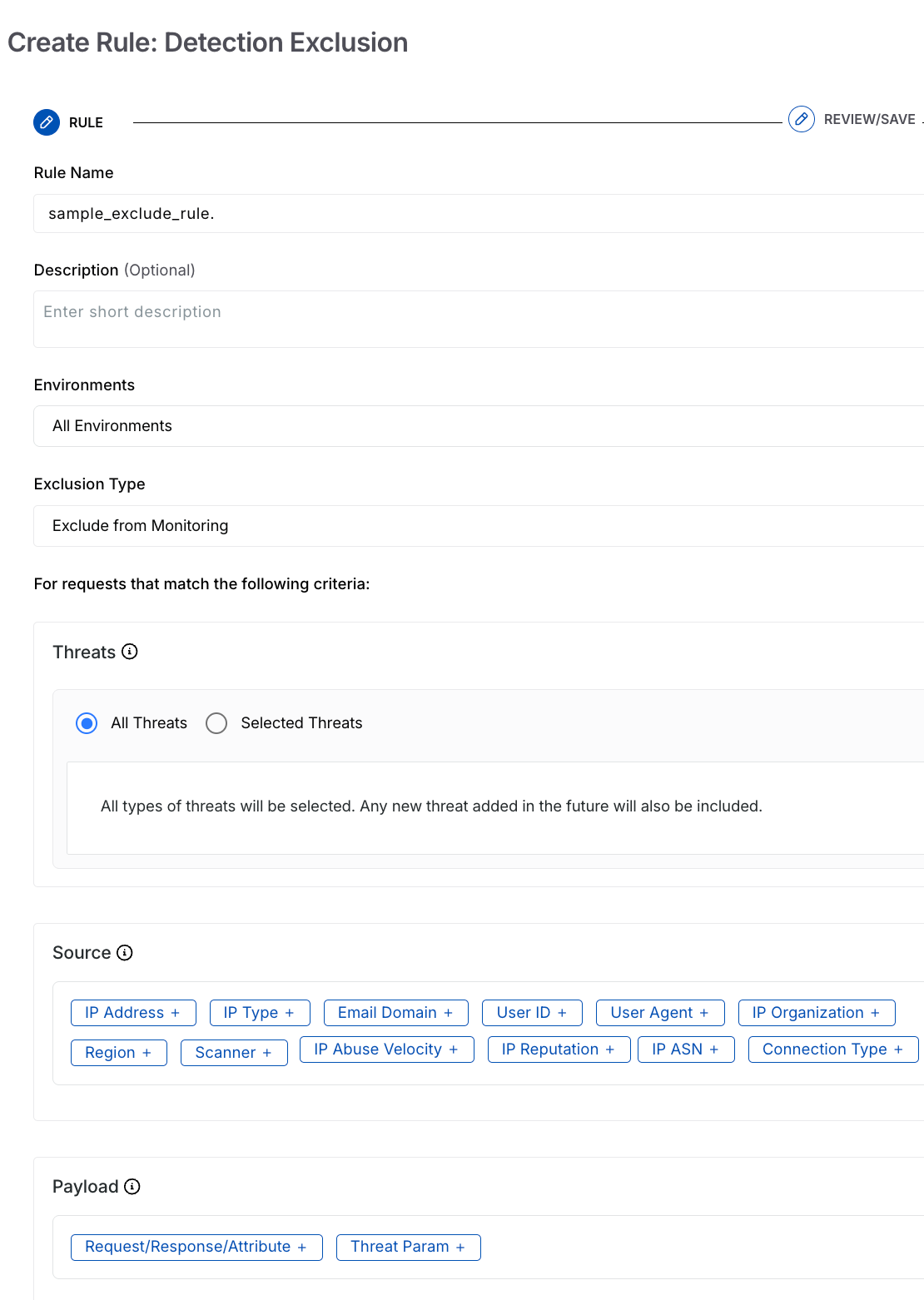
In the Create Rule: Detection Exclusion slide-out panel, complete the following steps:
Rule Name — The name for the rule, for example, sample_exclude_rule.
(Optional) Description — The summary of the rule’s purpose or the type of traffic it controls.
Environment — The environment from which you wish to exclude events, for example, All Environments.
Exclusion Type — The type of exclusion you want to configure, for example, Exclude from Monitoring. For more information, see Supported Exclusion Types.
Note
The Exclude from Blocking and Exclude from Allow options are only available for TPA version 1.49.0 and above.
You can select one or more exclusion types according to your requirements.
The availability of the source, the payload, and the target attributes below depend on the exclusion type you select.
Threats — Specify the threats that you wish to take action on:
All Threats — Apply the rule to all threats.
Selected Threats — Apply the rule to selected threats.
Source — Specify the source criteria you wish to apply the rule to. For example, IP Address → All External IPs. The following table describes the supported sources available for creating an exclusion rule in Traceable:
Source
Description
IP Address
Restrict or allow traffic from specific internal or external IP addresses.
IP Type
Control traffic based on IP type, such as Anonymous VPNs, bots, or scanners.
Scanner
Manage traffic originating from automated scanning and testing tools, such as Traceable AST and similar security scanners.
Email Domain
Limit requests originating from specific email domains or domain ranges associated with an organization.
User ID
Manage traffic using specific user IDs or user ID patterns defined through regular expressions (regex).
User Agent
Restrict requests based on user-agent patterns that identify automated clients, scripts, or bots.
IP Organization
Control traffic from known organizations or entities that commonly generate high API request volumes.
Connection Type
Enforce limits based on the connection source, such as corporate networks or data centers.
IP ASN
Restrict traffic from specific Autonomous System Numbers (ASNs) representing network providers.
IP Abuse Velocity
Limit requests from IPs exhibiting unusually high or abusive API request rates.
IP Reputation
Control traffic from IPs flagged as high risk by threat intelligence sources.
Region
Apply limits based on geographic location to manage region-specific traffic patterns.
Note
All Sources except IP Abuse Velocity and IP Reputation have an Exclude check-box corresponding to their value field.
When you select that check box, Traceable applies the exclusion rule on all values except the ones you choose.
Payload — Specify the Payload on which you want to apply the rule. You can select one or more payloads available for creating an exclusion rule in Traceable, as discussed below:
.png)
Exclusion Rule Payload
Threat Param — This option allows you to evaluate specific components by specifying additional key-value conditions associated with detected threats. You can use it to apply rules with greater precision based on threat metadata, ensuring targeted filtering. It includes the following components:
Field
Description
Key
Selects the threat attribute to evaluate, for example, Threat Type
Operator
Defines how the selected key is evaluated, for example, matches exactly.
Value
Specifies the values to include. Choose all values or narrow the scope to specific ones.
Request Payload — This option allows you to define conditions based on specific parts of an incoming request. It includes the following components:
Field
Description
Key (Component)
Selects the request component, for example, Host, Header, URL/Path, Query Parameter, or Body Field.
Operator
Defines how the component is evaluated, for example, matches exactly.
Value
Specifies the value to match against, for example, a header or parameter value.
Request / Response / Attribute — This option allows you to evaluate specific components from the Request, Response, or Attributes using defined operators and values. You can use it to build conditions based on URLs, headers, parameters, and payload fields. For more information, see Understand Payload Match.
Field
Static Payload Match
Dynamic Payload Match
Component
Selects a data source from the request, response, or attributes.
Selects data sources from the request, response, or attributes.
Operator
Defines how the selected data source is evaluated.
Defines how the selected data sources are evaluated.
Value
Specifies a fixed value for comparison.
Specifies another data source for comparison.
Mode
Defines evaluation using a static value.
Defines evaluation using attribute-to-attribute comparison.
Note
The availability of Dynamic toggle depends on the exclusion type you select above.
The availability of Request/Response/Attribute payload depends on the exclusion type you select above.
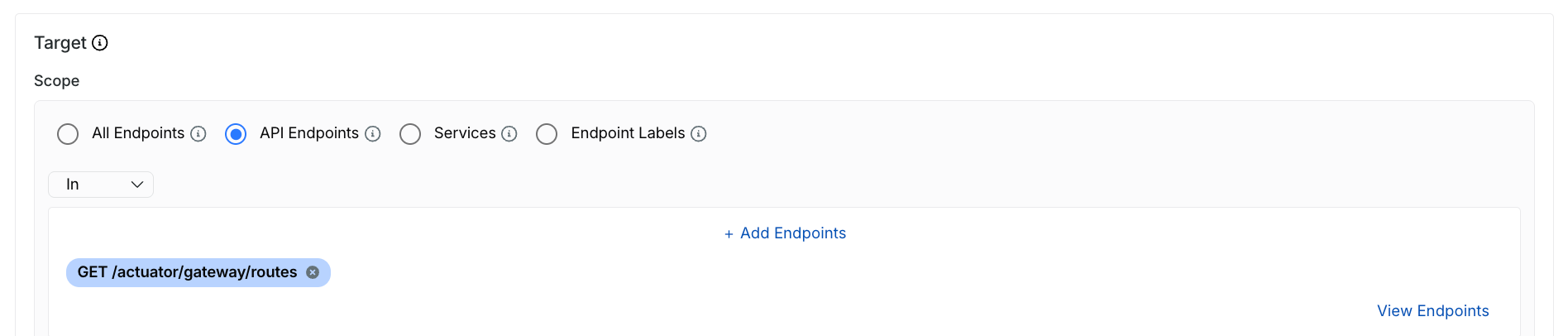
Target — Specify the endpoint scope to which the exclusion should apply, such as All Endpoints. You can select one or more APIs or the scope to which the rules should apply. The rule applies to all the underlying APIs and Services. The following table describes the supported targets available for creating an exclusion rule in Traceable:
Exclusion Rule Targets
Targets
Description
All Services
Apply the rule across all services that Traceable discovers and monitors.
Services
Apply the rule to one or more specific services. You can search or filter services based on your requirements.
All Endpoints
Apply the rule to all endpoints within the selected service(s).
API Endpoints
Apply the rule to specific API endpoints. This allows granular control at the endpoint level.
Endpoint Labels
Apply the rule to endpoints associated with specific labels, enabling logical grouping and reuse across APIs.
URL Regex (Optional)
Further restrict rule scope by matching endpoint URLs using regular expressions, for example, /login.
Note
The availability of the target attributes below depend on the exclusion type you select.
Once you have configured the above criteria, click Next.
Step 2 — Review and Save
In the Review and Save step, review the attributes you configured in the Criteria step and click Submit. You can try out a hands-on demo to create an exclusion rule policy in Traceable, as shown below.
Demo
The following interactive demo walks you through the steps to navigate and create exclusion rules under Protection.
Exclusions view
The exclusion rule should be visible on the Exclusions page. You can perform the steps above to create multiple rules.
Exclusions View
Actions on exclusions
You can also perform the following actions on the policies by clicking the Ellipse (![]() ) icon corresponding to a rule:
) icon corresponding to a rule:
Edit — Add or remove attributes as needed.
View — View a rule to identify the attributes Traceable uses to exclude specific attacks or threat actors.
Clone — Clone a rule to create a copy of an existing rule with the same values as the existing rule.
Reset — Reset the rule to default.
Change Logs — Log the changes of each activity occurring within the exclusion rule created.