Threat Modeling in Traceable helps you identify security risks and design mitigations before attackers can exploit those risks. In dynamic, cloud-native environments, your application architecture may change frequently, and manually maintained threat models can quickly become outdated. When these manual models do not accurately reflect runtime behavior, you risk missing undocumented APIs, unexpected service interactions, and evolving trust boundaries.
To address the issues above and improve your security posture, Traceable’s threat modeling builds on your application’s runtime visibility. Instead of modeling how your application should work, Traceable models your application’s actual behavior based on production traffic. This ensures that your application’s threat analysis reflects real services, APIs, and data flows.
What will you learn in this topic?
By the end of this topic, you will understand:
The role of runtime-derived architecture in threat modeling.
The relationship between API discovery and risk analysis.
The STRIDE framework and its application in Traceable.
The different scoping levels available for the STRIDE framework.
The available export options for integrating threat models into your workflows.
Runtime architecture and API discovery
Threat modeling in Traceable is grounded in the platform’s inherent capabilities. Traceable continuously observes production traffic across your assets (APIs, services, domains, and MCP primitives). From this determination, it reconstructs the runtime architecture and API inventory. The resulting application flow map illustrates how components in your application communicate under actual operating conditions.
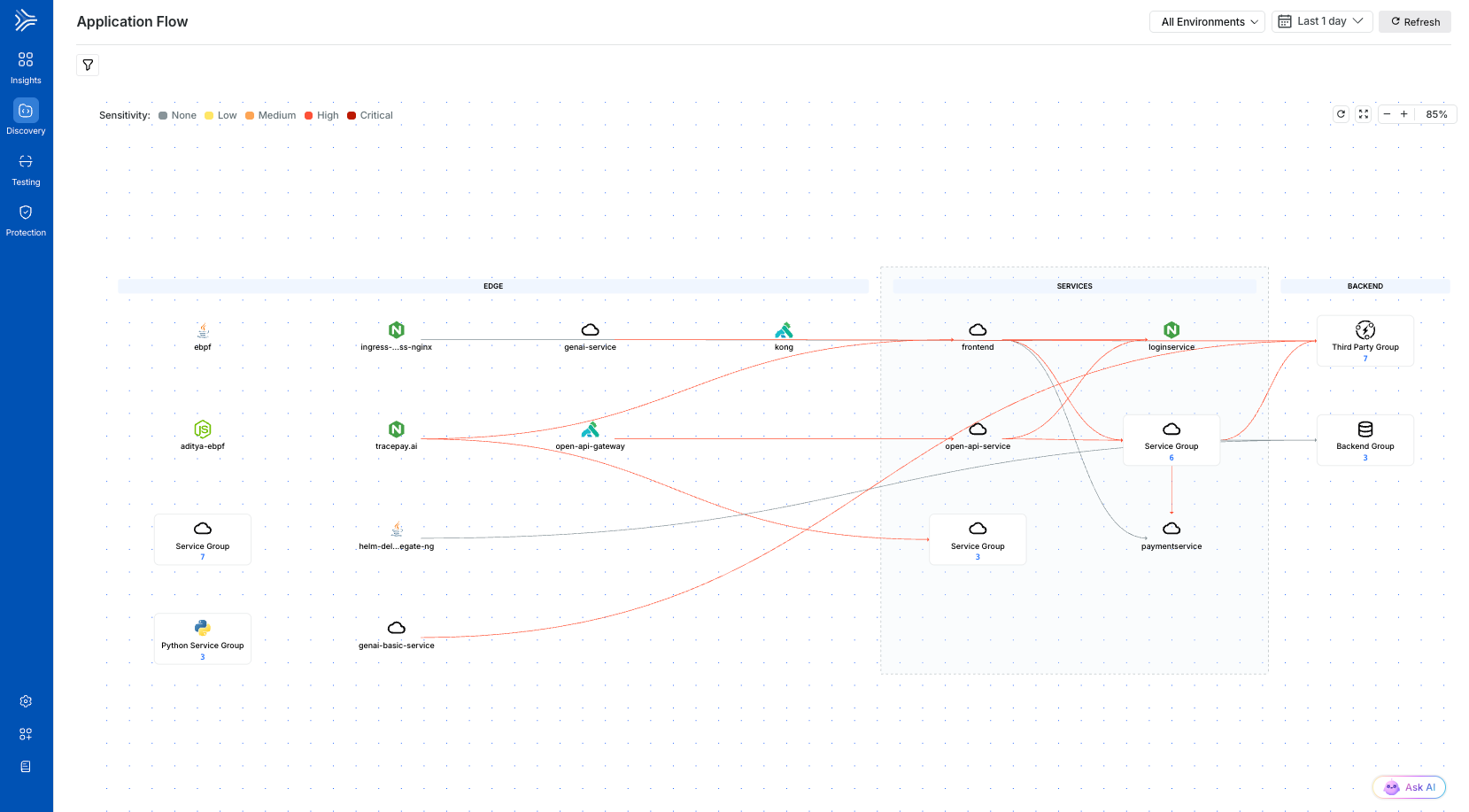
Application Flow
The architecture is organized into three logical layers:
Layer | Description |
|---|---|
Edge | This represents the externally reachable entry points, such as API gateways, load balancers, and ingress controllers. These define your application’s external exposure surface. |
Services | This represents application components that process requests and execute business logic. Traceable identifies services based on runtime communication patterns, request handling behavior, and identity propagation. |
Backend | This represents databases, storage systems, and third-party integrations identified through outbound communication(s). |
For more information on these layers, see Application Flow.
In addition to the above flow, Traceable derives asset-level intelligence and models the risk from observed traffic. For more information on risk score derivation, see Risk Score.
For each discovered service, Traceable identifies the:
Observed API paths and HTTP methods
Authentication mechanism in use
Request and response structures based on the runtime payloads
Exposure level, such as internal or external
Sensitive data flowing through the asset
For more information on these assets, see All Assets.
This runtime-based architecture identification and asset context form the foundation for threat analysis. Traceable continuously updates these capabilities as your application and environment evolve.
Threat modeling capabilities
In addition to discovery, threat modeling applies structured risk analysis to your application architecture. Traceable uses the STRIDE framework to categorize and evaluate potential security risks. STRIDE is a structured threat modeling framework that groups threats into six categories, enabling you to systematically assess risks to identity, data integrity, auditability, confidentiality, availability, and authorization.
The six categories in STRIDE are:
Threat Category | Security Property | Description |
|---|---|---|
Spoofing | Authentication | Impersonating a user or service |
Tampering | Integrity | Unauthorized modification of data in transit or at rest |
Repudiation | Non-repudiation | Inability to trace or prove actions due to insufficient logging |
Information Disclosure | Confidentiality | Exposure of sensitive data |
Denial of Service | Availability | Disruption or degradation of availability |
Elevation of Privilege | Authorization | Gaining higher access rights without authorization |
Once Traceable establishes the runtime architecture and API inventory, you can evaluate the assets and data flows across these categories. You can scope threat modeling to the following levels within this inventory:
Level | Description |
|---|---|
Application Level | Analyze system risks across your application architecture, including externally exposed components and trust boundary crossings. |
Service Level | Analyze risks for a specific service and evaluate its inbound and outbound interactions, authentication patterns, and dependency risks. |
Asset Level | Analyze individual assets based on observed request and response behavior, especially for sensitive or external ones. |
Traceable’s analysis, based on runtime-derived context, links risks to actual operational behavior rather than to assumed design intent. Since the model is created from live traffic, it provides an accurate, current view of your environment, eliminating the need for manual diagram creation.
Export and workflow integration
Traceable enables you to export generated threat models in OWASP Threat Dragon format to support collaboration, extended analysis, or integration with existing documentation processes. The exported artifact includes the architectural structure and contextual metadata identified from runtime data and observations.